One of the best things about business conferences is that you get a chance to know people and companies you perhaps would not have met otherwise. This interview is a result of an earlier encounter with Detectify, a Swedish company offering a SaaS based web application that analyzes and audits the security status of your website. I met them first at the Web Summit in Ireland and in January finally interviewed Fredrik Almroth, one of the co-founders who, among other things, hacked Google.
Where did you gain your technical skills to become a hacker and what lead to your interest in security and hacking?
Fredrik Almroth: I started back in school and there were all these viruses going around and they were all written in a scripting language called Visual Basic Scripting so I thought it was curious. I started to learn coding in Visual BS and Batch scripting and the Internet was becoming wider and wider, thus HTML was a natural step to learn. I started to hang out around security communities and that’s when I learned most of the basic stuff on IT security back then at least.
What’s your daily schedule like?
F.A.: I’m a technical guy and one of the founders of Detectify. I’m an IT security researcher and partly a developer meaning I will find vulnerabilities in software and I’ll go on and add it to the scanner. One day a week I research in order to find new vulnerabilities and the rest of the time I’m maintaining our service and keeping it up to date. To find security threats on the application you need to know what system is in place, so that’s another step in finding out what piece of software is running on this website. Once you have this piece of links withdrawn and we know which technologies are applied then we can start looking for vulnerabilities. I do a bit of everything in this soup.
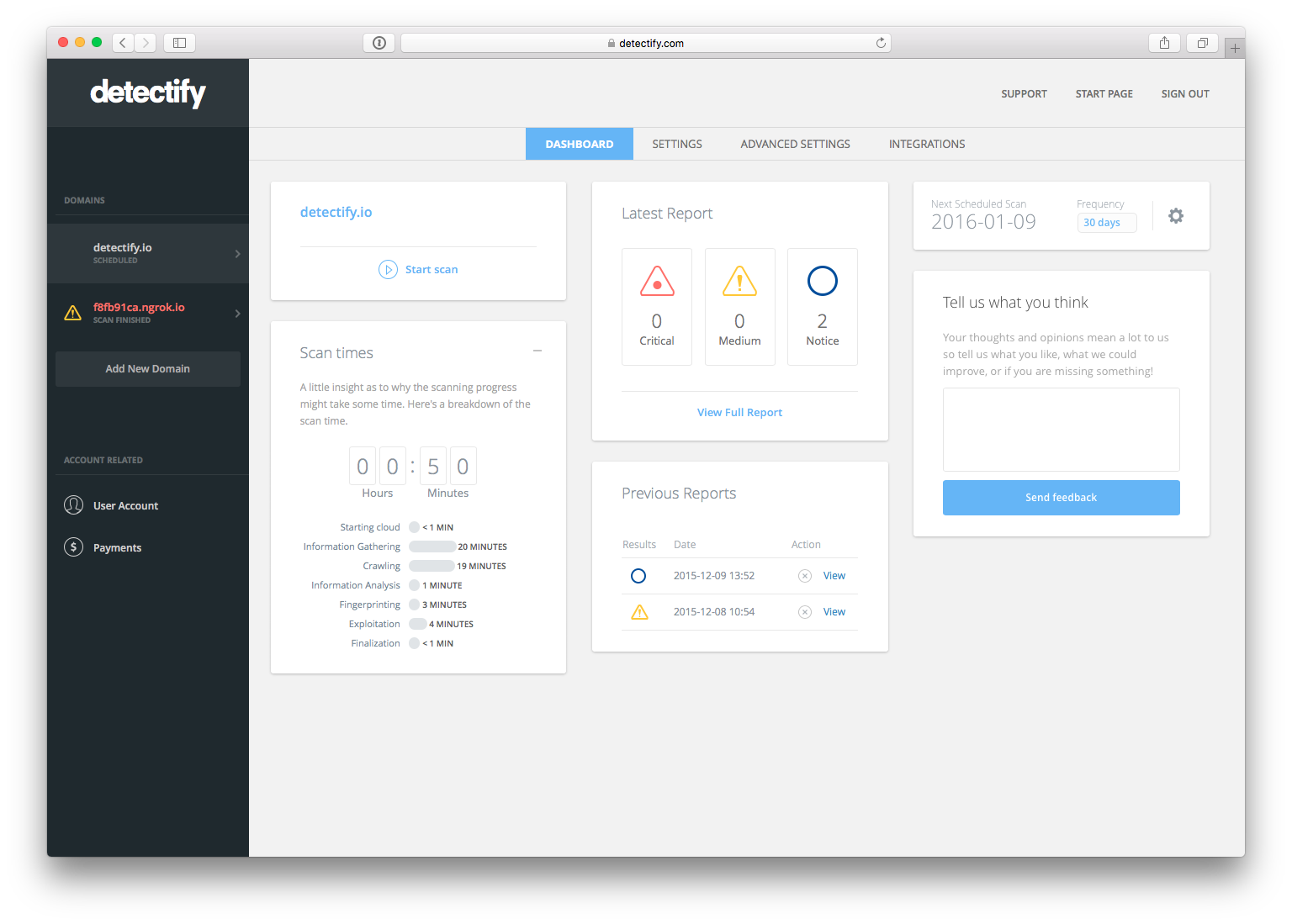
What is Detectify?
F.A.: We started Detectify at the end of 2012, we do IT security as a service. You come to us, add your website in our application and we start monitoring it for IT security threats. We do ongoing penetration tests against your application and whenever we find a vulnerability you’ll get an email or a notification, so it’s an automatic hacker for finding these vulnerabilities in software. The service tests your website against hundreds of vulnerabilities (covering OWASP Top 10) and creates a report of the identified vulnerabilities a hacker could use to access your website and customer data. We do this more as a continuous service, trying to find vulnerabilities as they come by when something is found while for other vendors it’s often one scan and you get one report. That’s how we are trying to differentiate.
What motivated you to hack Google?
F.A.: Google had this initiative that let anyone hack them legally and not be prosecuted as long as they get to know any vulnerabilities that are found. In return, they compensate you. So I and a friend, Mathias Karlsson, we started looking into Google’s servers and we were playing around for a few hours and found some interesting stuff. It turns out this old toolbar, the Google toolbar for IE search, it’s like this bundle that often got installed back in Windows XP times. We found that it was old and they didn’t maintain it anymore and we found the way to upload our own buttons for this old, ancient piece of software, a toolbar. And we figured out a way for Google to reveal their internal files from their servers so I could see any user accounts, source code, session cookies and anything really.
Related Articles: “IS CRYPTOCURRENCY THE NEW WAY WE BUY AND SELL?“
“TEACHING GIRLS TO CODE IN STYLE: JEWELBOTS“
We reported it to Google very quickly. Whatever files we found from Google servers were actually indexed by Google search so if you look it up it would actually show up in results. The more we kept digging in, the more viruses we actually found out, so we reported it and after 15 minutes they got back and said, “wow, this is huge.” That was a fast response where we were told we shouldn’t tell anyone before it was fixed. There were conversations back and forth and eventually they decided it would be okay for us to talk about it and we made a blog post explaining what we did and why we did it. It was published in the Hacker News and was praised by Silicon Valley and other big companies.
Do you think the Internet or maybe some of its services is broken? Why?
F.A.: I would say it’s getting better in a sense, but today people are building up more and more complex systems, multiple layers of software and if there’s a vulnerability in one of these pieces of software, you’re still vulnerable. Even though the overall tech stack is getting better it doesn’t mean that websites are necessarily getting better or more secure. But regarding the pieces of software on the Internet… that’s fundamentally broken, I’d say that HTTP, a protocol that transfers the web basically, what the web is built on, that has been broken for ages. And just now we’re starting to see HTTP2, a new technology that’s going to save it, or so they say, but it’s still very complex so we haven’t seen any new vulnerabilities in that protocol yet.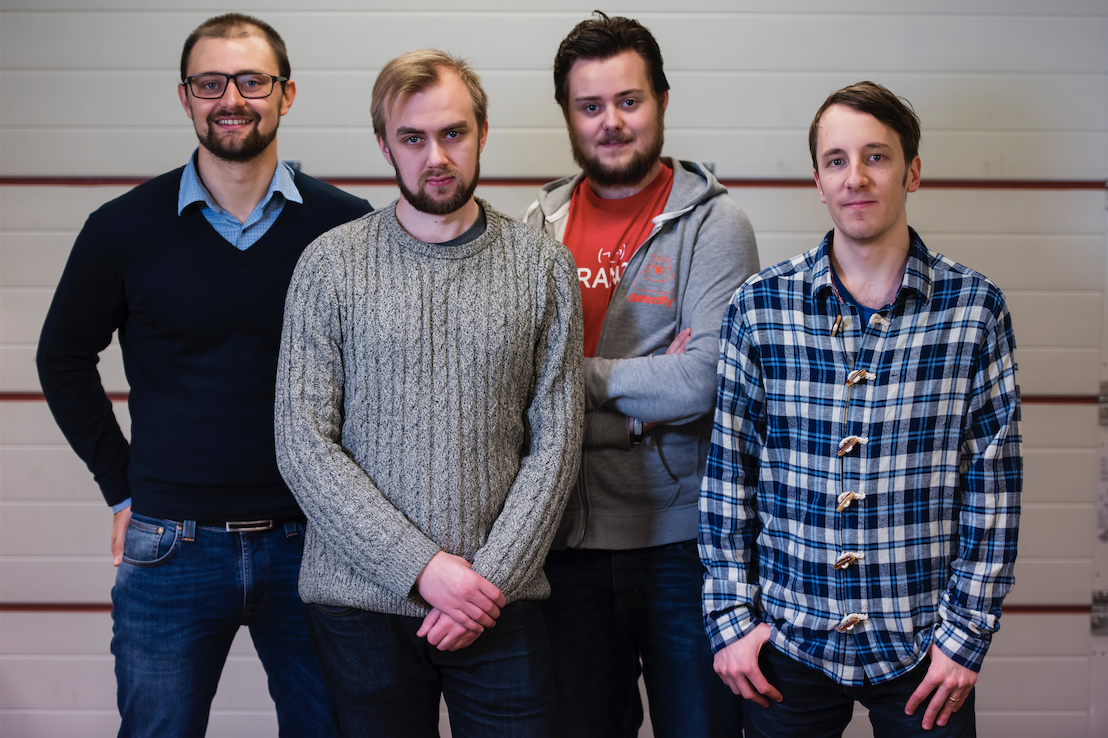
In the Photo: The Detectify Team
What issue is getting too little attention at the moment?
F.A.: Cookies are a big issue and DNS and domain names and how they are unencrypted. I think encryption is the most important thing that lot of people talk about but it’s not getting fixed in a good way. Think of emails, for example. You won’t even know if it’s sent over an encrypted channel or not even if it is an opportunistic encryption, meaning that if I were to see your encrypted traffic I could still see some pieces of information like a recipient and so forth.
Email security is something no one really talks about, there are some good security practices, there are some good pieces of software that makes it hard to crack but it’s not widely adopted and I think people haven’t heard about PGP. Laymen haven’t heard about it and I think mostly technical people have. I believe it would solve a lot if it was more widely adopted.
What simple steps should the average person take to be better secured?
F.A.: To be sane about it, you shouldn’t use the same password across multiple sites, especially for an email account. A very common thing for organized crime is to hack smaller websites and e-commerce sites, they get emails connected to encrypted passwords, the thing is these encrypted passwords can be hacked so you can see their content. Say you were to have a password: 1234 on some website you used once to buy a pair of shoes. They will then take your email address and try other services you might have signed up for. And if this was your email account then it’s game over because they will access anything, Facebook, Twitter, whatever. So having a diverse set of different passwords is a minimum. (Note: Using password managers like 1Password solves the problem of managing multiple passwords.)
If Oracle were to be applying new practices and such I think a lot of software would be better.
What do you think of Snowden?
F.A.: It was a good thing he did what he did, so people could see how deep surveillance goes. On the other hand, considering diplomacy between the U.S. and other countries, what you see in the media has been from Snowden’s perspective, but you never see how that affects nations on that level. I think it’s good for people but you don’t really see the actual consequences it might not have cost, or it might have cost. I think it’s a one-sided story, unfortunately, and the NSA can’t talk about it.
Can you name a person you think is very insightful in a space you operate in?
F.A.: Mikko Hyppönen, from F-Secure, he’s super smart. And Bruce Schneier, he is into a security as a whole, not just IT security.
Besides excelling in technical solutions, what organizations and individuals would you like to see taking a stand and what’s the thinking we should embrace to develop technology to the next level?
F.A.: Oracle bought Sun Microsystems and they have Java, they are a big company but they have an old way of looking at the systems, software and security. If Oracle were to be applying new practices and such I think a lot of software would be better. So now, Android is worldwide and is made by Google and it’s based on Java by Oracle. The thing is, you’re not allowed to do research in Java to find new vulnerabilities because you would get a lawsuit. So if you‘re trying to figure out how a specific functionality in Java works, that’s breaking the terms of their service.
So that means hackers can’t help by fixing the issues?
F.A.: More or less. The bad guys will do it anyway but those with good intentions won’t be able to without going through like a legal process. And so much technology is based on Oracle.
Share an idea that drives you and shortly describe what’s the next big thing?
F.A.: Everyone sees that IT security is a big problem and you see it in the media once a week. That’s what we’re trying to solve, we figured that the Internet is broken and that’s why we founded Detectify, we thought we could make the Internet a better place. So, vulnerabilities come by every day but people are also quick to weaponize themselves against.
_ _
All photos courtesy of Detectify